Disclaimer: Information found on CryptoreNews is those of writers quoted. It does not represent the opinions of CryptoreNews on whether to sell, buy or hold any investments. You are advised to conduct your own research before making any investment decisions. Use provided information at your own risk.
CryptoreNews covers fintech, blockchain and Bitcoin bringing you the latest crypto news and analyses on the future of money.
DOJ Claims Tornado Cash Developer Implemented 250 Modifications to the Protocol: Is the Defense of Immutable Code No Longer Valid?
The core legal argument from the DOJ in the Roman Storm crypto case has never been that coding itself constitutes a crime. Rather, it asserts that maintaining operational control over a platform that handles over $1 billion in illicit transactions—while deliberately opting not to implement viable anti-money-laundering measures—amounts to operating a criminal enterprise.
This distinction is what elevates the significance of this case beyond just Tornado Cash.
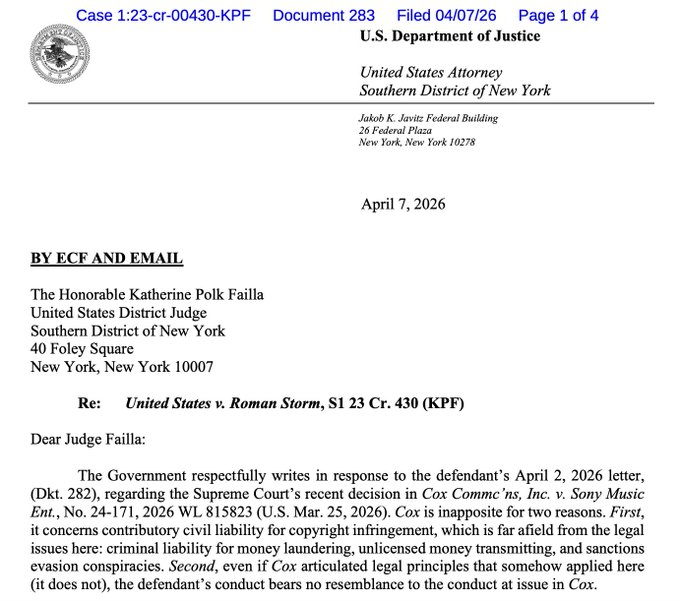
On Tuesday, prosecutors submitted a letter dismissing Storm’s effort to use a March Supreme Court decision in Sony Music v. Cox Communications as a basis for dismissal.
The DOJ described the comparison as “inapposite”—and the rationale behind this dismissal clarifies the level of developer involvement that incurs federal criminal liability under the existing enforcement framework.
The unresolved issue remains: what is the legal threshold for DeFi developers who upgrade protocols, oversee governance, and selectively address compliance inquiries? Following Tuesday’s filing, that threshold remains unclear—and prosecutors are advocating for Storm’s retrial to establish it.
Key Takeaways:
- The Dismissal Attempt: Storm’s legal representatives referenced the Supreme Court’s Cox ruling—which protected the ISP from liability for users’ copyright violations—as a precedent for dismissing criminal charges. DOJ prosecutors dismissed the analogy as irrelevant to Storm’s actions.
- The Control Argument: Prosecutors documented over 250 modifications made to the Tornado Cash infrastructure during the charged timeframe, directly contradicting Storm’s defense that the protocol was immutable code beyond his influence. This operational history is crucial to the money laundering conspiracy allegation.
- The Partial Conviction: In August 2025, a jury found Storm guilty of conspiracy to operate an unlicensed money-transmitting business but was deadlocked on the charges of money laundering conspiracy and sanctions evasion—two counts that prosecutors now seek to retry in October 2026.
- The Privacy Protocols Precedent: The DOJ’s framing—that developers who make changes and knowingly neglect compliance measures are operators, not bystanders—directly applies to any upgradeable DeFi protocol with identified founders or core teams.
- The Exposure: Storm could face a prison sentence of up to 40–45 years if convicted on all charges. The retrial will focus on the two deadlocked charges; the money transmitting conviction remains intact.
- What to Watch: The conference between Storm’s defense and Judge Katherine Polk Failla’s court will determine if October 2026 will be set as a definitive retrial date—the specific scheduling order will be the next legal trigger that either confirms or shortens the timeline.
Explore: The best pre-launch token sales with asymmetric upside potential
What the DOJ’s Cox Rejection Actually Establishes – and Why the ‘Immutable Code’ Defense Is Running Out of Road
Storm’s legal team made a specific comparison: the Supreme Court determined that Cox Communications should not be held liable for its users’ infringing activities because Cox maintained a robust, 98%-effective termination policy for repeat offenders.
The argument posited that Storm, similar to Cox, was a neutral infrastructure provider. Prosecutors dismantled that analogy in a single filing.
The DOJ’s letter to Judge Failla highlighted that Cox actively discouraged the illegal activities occurring on its network—whereas Storm and his co-conspirators at Tornado Cash did the opposite.
 Source: DOJ
Source: DOJ
Prosecutors asserted that Storm “actively misled victims in response to inquiries, claiming he had limited control over the protocol when, in fact, he and his co-conspirators made over 250 modifications to Tornado Cash infrastructure during the charged period and explicitly discussed—but chose not to implement—feasible measures to mitigate criminal activity on their platform.”
This last clause carries significant legal weight. Under the money laundering and unlicensed money transmission statutes in question, the issue is not whether a developer wrote code—it’s whether they operated a system they were aware was being used for money laundering, had the ability to restrict that use, and opted not to.
The Bank Secrecy Act’s anti-money-laundering compliance requirements pertain to operators, not passive observers. Prosecutors maintain that Storm was an operator by every functional standard.
“In summary, the defendant’s response to the criminal use of his company was mere window dressing at best and outright misdirection at worst,” stated the prosecutors’ letter to Judge Failla, submitted on Tuesday.
The August 2025 jury conviction on the unlicensed money transmission charge already dismissed Storm’s passive-developer argument once.
The October 2026 retrial will directly address the money laundering conspiracy and sanctions evasion charges—the counts where the jury was deadlocked, not where it acquitted. This distinction is significant: a deadlock indicates that twelve jurors could not reach a unanimous decision, not that the evidence was insufficient for a conviction.
Discover: The Best Crypto Presales Live Right Now
The post DOJ Says Tornado Cash Developer Made 250 Changes to the Protocol: Is the Immutable Code Defense Dead? appeared first on Cryptonews.
