Disclaimer: Information found on CryptoreNews is those of writers quoted. It does not represent the opinions of CryptoreNews on whether to sell, buy or hold any investments. You are advised to conduct your own research before making any investment decisions. Use provided information at your own risk.
CryptoreNews covers fintech, blockchain and Bitcoin bringing you the latest crypto news and analyses on the future of money.
Kraken Claims It Is Being Blackmailed Regarding Compromised Cryptocurrency User Information and Declines to Comply
On Monday, Kraken announced that it is facing extortion from a criminal organization that possesses videos of its internal systems containing customer information, and the cryptocurrency exchange has publicly declined to comply with their demands.
Chief Security Officer Nick Percoco revealed the threat through X on April 13, 2026, indicating that the company is collaborating with federal law enforcement across various jurisdictions to pursue arrests.
This refusal is a prudent decision. It also serves as a strategic institutional message at a time when trust in exchanges is inherently vulnerable.
Key Takeaways:
- What was breached: Internal systems containing customer data were accessed through insider recruitment – there was no complete system compromise and customer funds were not at risk, as stated by Kraken.
- Scope: Approximately 2,000 individuals may have had their information accessed, representing about 0.02% of Kraken’s total user base; all impacted users have been notified.
- Extortion mechanism: Criminals are threatening to release videos of Kraken’s internal systems and disseminate fragments of customer data to media and social platforms unless their demands are met.
- Kraken’s response: Percoco publicly stated: “We will not pay these criminals; we will not ever negotiate with bad actors” – and confirmed ongoing engagement with federal law enforcement across multiple jurisdictions.
- Insider pattern: A February 2025 incident involved a similar video shared on a criminal forum; in both cases, an individual from within the company was identified.
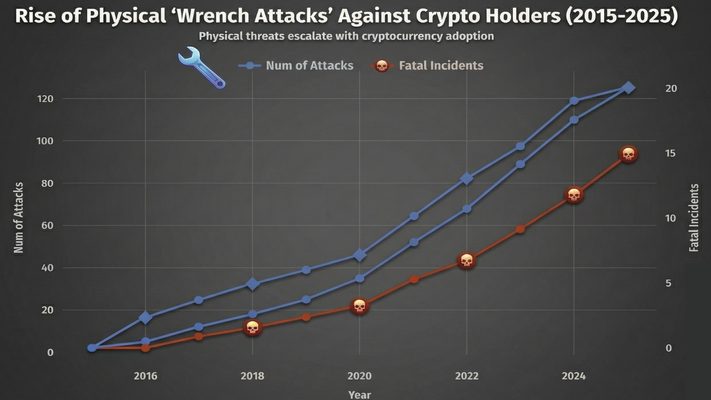
- Sector context: Wrench attacks targeting personnel in the crypto industry rose by over 75% year-over-year, with CertiK attributing more than $40 million in confirmed losses to such attacks last year.
- Watch: The potential for law enforcement arrests and how Kraken’s postponed IPO timeline will manage the reputational impact from a second consecutive security incident.
How Kraken Crypto Breach and Extortion Mechanics Actually Worked
This was not a credential-scraping exploit or a vulnerability in the protocol. The entry point for both the February 2025 incident and the current extortion threat was insider recruitment; compromised individuals within Kraken’s organization provided access to internal systems, allowing for reconnaissance rather than a complete breach.
The access appears to have been read-only, sufficient to capture customer data on video without triggering immediate detection.
Percoco confirmed that Kraken received a tip regarding a video displaying sensitive customer information from its internal crypto systems, the same method used in the February 2025 case, when a similar video appeared on a criminal forum.
In both situations, an internal actor was identified. The criminals are now threatening to distribute those videos and related customer data to local media and across social networks unless Kraken meets their unspecified demands. The exact amount of the extortion demand has not been publicly revealed.
Kraken Security Update
We are currently being extorted by a criminal group threatening to release videos of our internal systems with client data shown if we do not comply with their demands. It’s important to start with the most important points: our systems were never…— Nick Percoco (@c7five) April 13, 2026
The pattern described by Percoco is intentional and scalable. “We have been collaborating with industry partners and law enforcement to investigate and disrupt insider recruitment efforts targeting not only crypto companies, but also gaming and telecommunications organizations,” he stated.
This is not opportunistic hacking. It represents a coordinated recruitment infrastructure operating across high-value data sectors, and Kraken is explicitly identifying it as such, which is significant for how the industry should respond.
Emerging vectors for crypto theft increasingly focus on infrastructure access rather than on-chain exploits, and insider recruitment aligns with that same threat profile.
Discover: The best pre-launch token sales
What User Data Was Actually Exposed – and What That Enables
Kraken has not publicly detailed which categories of data were captured in the videos, including KYC documentation, wallet addresses, transaction history, or account metadata.
What is confirmed: approximately 2,000 individuals had their information accessed, and Kraken states it has already reached out to everyone at risk. The access was read-only, and internal systems were not compromised in the broader sense of data being exfiltrated at scale.
The practical risk for affected users is not account takeover; no funds were accessed. The risk lies in targeted social engineering and physical exposure.
(Source – TRM Labs)
With names, addresses, and account-level data in the hands of criminals, affected users become targets for the same wrench attack vector that CertiK tracked, resulting in over $40 million in losses last year.
This figure is likely an undercount, given the tendency for underreporting. Kraken’s outreach to affected users is the appropriate procedural step; whether that outreach included specific security guidance, hardware key recommendations, address changes, or increased vigilance is not confirmed.
Discover: The best crypto to diversify your portfolio with
The post Kraken Says It Is Being Extorted Over Stolen Crypto User Data and Refuses to Pay appeared first on Cryptonews.
