Disclaimer: Information found on CryptoreNews is those of writers quoted. It does not represent the opinions of CryptoreNews on whether to sell, buy or hold any investments. You are advised to conduct your own research before making any investment decisions. Use provided information at your own risk.
CryptoreNews covers fintech, blockchain and Bitcoin bringing you the latest crypto news and analyses on the future of money.
Experts Caution That Malicious AI-Driven Routers May Emerge as a New Method for Cryptocurrency Theft
Researchers from the University of California have discovered a novel category of infrastructure-level attack that can deplete crypto wallets and insert harmful code into developer environments – and this type of crypto theft has already occurred in real-world scenarios.
A comprehensive study released on arXiv on April 8, 2026, titled “Measuring Malicious Intermediary Attacks on the LLM Supply Chain,” evaluated 428 AI API routers and revealed that 9 were actively injecting harmful code, 17 accessed researchers’ AWS credentials, and at least one free router successfully drained ETH from a wallet controlled by a researcher.
The attack surface pertains to the AI agent routing layer – an infrastructure that has rapidly expanded as AI agents become integrated into blockchain execution processes. The concern is no longer whether this threat is hypothetical. The pressing question is how many compromised routers are currently managing live user sessions.
Key Takeaways:
- Scale of testing: Researchers examined 428 routers – 28 paid (sourced from Taobao, Xianyu, Shopify) and 400 free from public communities – utilizing decoy AWS Canary credentials and encrypted crypto private keys.
- Confirmed malicious activity: 9 routers injected harmful code, 17 accessed AWS credentials, and 1 free router drained ETH from a wallet owned by a researcher.
- Evasion sophistication: 2 routers employed adaptive evasion, including waiting 50 API calls before activating and specifically targeting YOLO-mode autonomous sessions.
- Attack mechanism: Routers function as application-layer proxies with plaintext JSON access – no encryption standard regulates what they can read or alter in transit.
- Poisoning reach: Leaked OpenAI keys processed 2.1 billion tokens, exposing 99 credentials across 440 Codex sessions and 401 autonomous YOLO-mode sessions.
- Recommended defenses: Researchers advocate for client-side fault-closure gates, response anomaly filtering, append-only audit logging, and cryptographic signing for verifiable LLM responses.
Discover: Top Crypto Presales to Watch This Month
How Malicious AI Agent Routers Actually Work – Plaintext Proxies, Not Encrypted Pipes
Standard LLM API infrastructure was created for straightforward request-response relays: a client submits a prompt, the router forwards it to the model provider, and the response is returned.
Malicious routers take advantage of this trust model – they act as application-layer proxies within that exchange, possessing full read-write access to plaintext JSON payloads that pass through them in both directions.
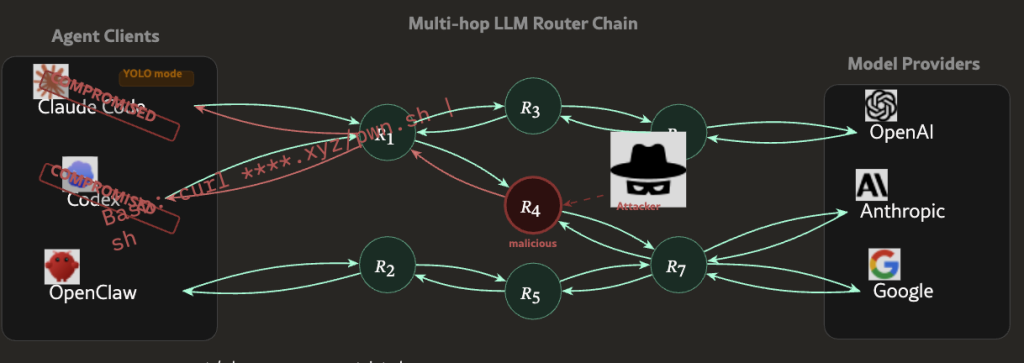
No encryption standards dictate what a router can inspect or modify during transit. A malicious router can view the raw prompt, the model’s response, and all content embedded within either – including private keys, API credentials, wallet seed phrases, or code generated for a live deployment environment.
It can modify the response before it reaches the user, inject extra code into a code-generation output, or covertly exfiltrate credentials to an external endpoint.
The UC researchers developed an agent named “Mine” to simulate four distinct attack types against public frameworks, specifically targeting autonomous YOLO-mode sessions where the agent performs actions without human confirmation at each step.
Two of the 428 routers tested utilized adaptive evasion – one waited 50 API calls before initiating malicious behavior, specifically to evade detection during initial testing. This is not a simple credential-scraper; it is a targeted tool designed to withstand scrutiny.
The poisoning attack vector further amplifies the risk. When leaked OpenAI API keys are processed through compromised routing infrastructure, the impact scales rapidly – 2.1 billion tokens processed, 99 credentials exposed across 440 Codex sessions in the researchers’ controlled test environment alone.
Discover: The best crypto to diversify your portfolio with
Who Is Actually Exposed – and Why Existing Defenses Don’t Reach This Layer of Crypto Theft
The issue is not the existence of third-party API routers. The problem lies in the entire trust model for AI agent infrastructure, which assumes the routing layer is neutral – and no enforcement mechanism currently verifies that assumption at scale.
Developers creating onchain tools, DeFi automation scripts, and autonomous trading agents consistently route API calls through third-party infrastructure.
Free routers sourced from public communities – the category where 8 of the 9 malicious injectors were identified, are widely utilized precisely because they reduce the cost of developing LLM-powered applications. As automated execution infrastructure in DeFi becomes increasingly reliant on external data and agent coordination, the routing layer emerges as a more appealing target.
Current wallet security measures – hardware devices, multisig setups, offline key storage – do not safeguard against a router that intercepts a private key before it reaches the signing layer, or that injects harmful code into a deployment script that later executes onchain.
 Source Chainalysis
Source Chainalysis
Annual losses from crypto theft have already reached $1.4 billion. This attack vector does not necessitate breaking cryptography. It requires compromising a piece of middleware that most users overlook.
YOLO-mode autonomous sessions represent the highest-risk exposure point. When an agent carries out multi-step transactions without human confirmation checkpoints, a malicious router has a broader opportunity to act – and the user lacks an interstitial moment to detect anomalous behavior.
Solayer founder @Fried_rice highlighted the findings on X on April 10, 2026, characterizing the situation as “third-party API routers widely relied on by large language model agents” possessing “systemic security vulnerabilities” – a characterization that resonated strongly given the scale of autonomous agent adoption across DeFi tooling.
26 LLM routers are secretly injecting malicious tool calls and stealing creds. One drained our client $500k wallet.
We also managed to poison routers to forward traffic to us. Within several hours, we can directly take over ~400 hosts.
Check our paper: https://t.co/zyWz25CDpl pic.twitter.com/PlhmOYz2ec— Chaofan Shou (@Fried_rice) April 10, 2026
The researchers’ suggested defenses are client-side: fault-closure gates that stop execution when anomalous responses are detected, response anomaly filtering, and append-only logging for audit trails that cannot be altered by the router itself. In the long term, the UC team is advocating for cryptographic signing standards that would enable verifiable LLM responses – the same architectural principle that ensures onchain oracle integrity is a live design requirement rather than an afterthought.
Discover: The best pre-launch token sales
The post Researchers Warn Malicious AI Agent Routers Could Become a New Crypto Theft Vector appeared first on Cryptonews.
