Disclaimer: Information found on CryptoreNews is those of writers quoted. It does not represent the opinions of CryptoreNews on whether to sell, buy or hold any investments. You are advised to conduct your own research before making any investment decisions. Use provided information at your own risk.
CryptoreNews covers fintech, blockchain and Bitcoin bringing you the latest crypto news and analyses on the future of money.
The Bybit Breach Explained: Details of the Incident, Perpetrators, and Future Implications
Friday’s Bybit breach marked a troubling day for the cryptocurrency sector — highlighting two significant issues.
Firstly, even platforms with robust security protocols are susceptible to sophisticated attacks. Secondly, the evolving tactics of North Korean hackers present a growing threat, with their thefts becoming larger and more frequent each year.
This incident represents the largest hack in the history of cryptocurrency, with $1.4 billion disappearing in an instant — easily surpassing the $625 million stolen from the Ronin Network nearly three years ago.
Here, Cryptonews will guide you through everything we currently know about the incident — including what transpired, who was behind it, and the broader implications for the industry.
The Hack
Shortly after reports of the breach began circulating, Bybit issued a statement on X confirming that “unauthorized activity” had been detected in one of its ETH cold wallets.
At that moment, a routine transfer was being executed to a hot wallet, and the transaction had undergone several checks beforehand.
Bybit CEO Ben Zhou was the last individual to authorize the transaction — and after conducting a series of security checks, he was satisfied that everything appeared to be in order. However, despite the correct destination being displayed for the transfer, behind-the-scenes manipulation resulted in the funds being redirected to the hackers’ wallet.
Chainalysis reported that the initial breach occurred through social engineering, stating:
“The hackers gained access to Bybit’s user interface by executing phishing attacks against the cold wallet signers, leading them to sign malicious transactions that replaced the Safe’s multi-signature wallet implementation contract with a malicious one.”
In a Spaces conversation on X, Zhou disclosed that he received a phone call from his chief financial officer thirty minutes after the transaction was completed.
“I could sense something was wrong because the person was just shaking … he could barely speak. ‘Ben, there was an issue … we may be hacked.’”
The CEO mentioned that he initially believed that 30,000 ETH — valued at approximately $82 million — was affected, but was later informed that 401,000 ETH had been stored in this cold wallet. All of it was gone.
“I experienced this overwhelming breathlessness; I couldn’t breathe. For about five seconds, I didn’t say anything. I thought to myself ten seconds later that I needed to snap out of it.”
Zhou stated he implemented rapid security protocols that had been practiced monthly — and he utilized a button that allowed him to alert everyone in the company, including top management. At that moment, he indicated that his primary concern was not to recover the $1.4 billion — but to safeguard Bybit’s reputation.
A livestream was quickly arranged so Zhou could address questions from Bybit clients, but there were two key points he wanted to emphasize to clients: all other cold wallets were secure, and the exchange was capable of covering the loss since customer assets are backed on a one-to-one basis.
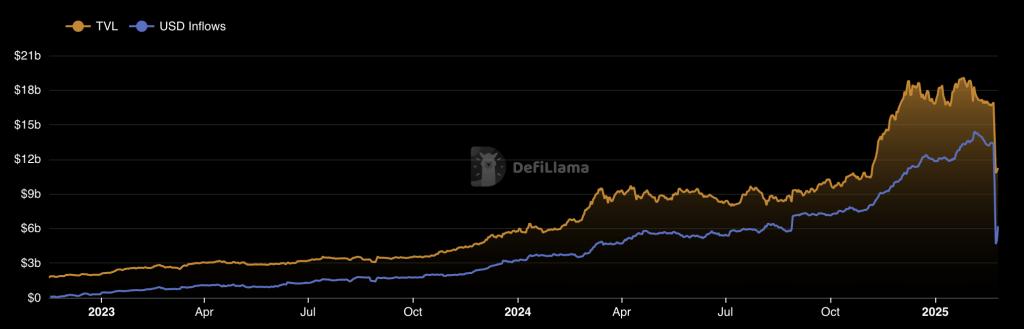 The total value locked on Bybit. Image: DeFiLlama
The total value locked on Bybit. Image: DeFiLlama
Before that broadcast commenced, Zhou sent a message to employees stating:
“Dear Bybuddies, understand that it’s a challenging time now. I appreciate that all of you are standing in line. It’s going to be a tough 24 to 48 hours that we will face, but I’m confident that we will make it through. Please ensure we remain professional and calm to all clients and external partners. We’ll do our best to maintain withdrawals. At the same time, I want to emphasize that even with this level of loss, all customer assets are covered. It’s time to respond to clients’ questions promptly and be there for our clients, and we will use transparency and communication to alleviate doubts from our clients.”
Zhou accurately anticipated what was forthcoming — and ultimately, it appears Bybit managed to fulfill that promise. The exchange later disclosed that it had processed an astonishing 350,000 withdrawal requests within the first ten hours of the hack… and 580,000 had been successfully completed by Saturday. Once that backlog was cleared, the company stated all of its systems were functioning normally.
Maintaining the appearance of “business as usual” was crucial, as many trading platforms have abruptly halted withdrawals in the past — and in the case of FTX, this was a precursor to a prolonged and complicated situation.
DeFiLlama data indicates Bybit had nearly $17 billion in total assets before the hack occurred, but this figure plummeted to $10.8 billion by Sunday as clients rushed to withdraw funds from their accounts. As of Tuesday, that amount had slightly rebounded — rising to $11.5 billion.
 Funds stolen by North Korea. Image: Chainalysis
Funds stolen by North Korea. Image: Chainalysis
The Hackers
As Bybit worked to reassure clients and the markets, on-chain investigators were also getting to work — identifying who was responsible.
Within hours of the $1.4 billion hack taking place, ZachXBT had uncovered conclusive evidence that the Lazarus Group was behind this exploit.
This group has close ties to the North Korean government, with U.S. officials asserting that stolen cryptocurrency ultimately gets laundered, cashed out, and used to finance the isolated state’s programs for developing ballistic missiles and weapons of mass destruction.
The Lazarus Group has been linked to some of the most significant hacks to impact the cryptocurrency industry in recent years — including the $234 million WazirX theft earlier this year, the $100 million stolen from both Atomic Wallet and Horizon, and the staggering $625 million taken from the Ronin Network.
While cryptocurrency transactions are traceable to a degree, mixers and decentralized exchanges enable these cybercriminals to obscure the source of funds, making it appear as though they have vanished without a trace. Reflecting on the Lazarus playbook following the Ronin attack, Chainalysis senior director of investigations Erin Plante stated:
“They move the funds very quickly and they route them through many different forms of obfuscation to reach a point where they can attempt to cash out swiftly. They hope investigations are several steps behind because they’re only going to keep the funds in a freezable state — like a stablecoin or a centralized exchange — for five or ten minutes. And they hope that they’ve gotten just far enough ahead of investigators, and mixed in just enough laundering, that the services won’t know where they trace back to.”
Arkham Intelligence has been monitoring the fate of the 401,000 ETH stolen from Bybit — mapping out a network of wallets where the cryptocurrency has been distributed thus far. It reported:
“The Bybit Hacker is making 2-3 transactions per minute, and pauses every 45 minutes for a 15-minute break. They transfer ETH from one address at a time, before moving on to the next one.”
So far, it appears the Lazarus Group has been exchanging this stolen Ether primarily for Bitcoin, as well as the DAI stablecoin. Decentralized exchanges, cross-chain bridges, and instant swap services that do not enforce Know Your Customer checks have been utilized to move funds across blockchains.
However, $1.4 billion is a substantial amount — and Chainalysis has cautioned that the hackers will not hesitate to allow some of this cryptocurrency to remain dormant for a short period.
“By delaying laundering efforts, they aim to outlast the heightened scrutiny that typically follows such high-profile breaches.”
BYBIT HACKER LAUNDERING FUNDS
The Bybit Hacker is making 2-3 transactions per minute, and stops every 45 minutes for a 15-minute break. They transfer ETH from one address at a time, before moving on to the next one.
Did Lazarus get an intern to clean their funds manually? pic.twitter.com/XCS16hMC3i— Arkham (@arkham) February 24, 2025
The Fightback
Bybit has now initiated a bounty program aimed at rewarding security experts who assist in recovering this stolen cryptocurrency — meaning they will receive 10% of any funds recovered. This translates to up to $140 million available for recovery.
However, progress has been relatively limited thus far. By Sunday, only $85 million of the funds taken by the Lazarus Group had been frozen or recovered… amounting to just under 5% of what’s missing.
On Monday, the exchange asserted that it has also managed to completely close the ETH gap of customer assets within 72 hours — adding that “strategic partnerships with companies like Galaxy Digital, FalconX, and Wintermute, along with support from Bitget, MEXC, and DWF Labs, helped Bybit replenish the reserves in record time.”
This was corroborated by a Hacken audit that confirmed the crypto platform — which is the world’s second largest in terms of trading volumes — “possesses sufficient reserves to cover customer assets 1:1 across the board.”
Bybit had introduced Proof of Reserves in direct response to the FTX breach — and at that time, stated “laying everything on the table deters a crypto exchange from engaging in secretive financial transactions.”
Zhou was asked on X whether he believes there is any chance his exchange will recover the stolen cryptocurrency — and if there is any merit in involving law enforcement agencies. He responded:
“We’ll do our best … I assume it will take a long, long time for the hackers to clean this money out. We hope that by creating enough difficulty for them, perhaps they might consider returning it at some point … the Singapore police are taking it seriously and have already escalated it to the Interpol level.”
Based on the current situation, any possibility of the Lazarus Group realizing the error of their ways and returning the cryptocurrency seems exceedingly unlikely.
The Threat
Chainalysis has been closely monitoring the Lazarus Group, and it is evident that their hacks on cryptocurrency exchanges are intensifying.
North Korea was responsible for approximately two-thirds of the funds stolen from this sector in 2024 — but this does not tell the entire story.
About $660 million was taken by Lazarus across 20 incidents in 2023, surging to $1.34 billion in 47 hacks last year. Just two months into 2025, this group has managed to break records — and that was through just one attack.
Attention is now shifting to whether such attacks can be prevented in the future — and whether cryptocurrency exchanges provide a secure environment for investors to store their assets.
Ledger CEO Pascal Gauthier has argued that trading platforms need to reevaluate their security measures entirely, and make a concerted shift to new approaches such as “Clear Signing.” On X, he stated:
“Security is not static — attackers are becoming more sophisticated, and our industry must stay ahead by implementing the highest business security standards to prevent the next, more refined attack.”
Clear Signing entails that details about a transaction are presented in a human-readable format, and Gauthier contends that Bybit’s exploit would not have occurred had this security layer been implemented.
Ledger has also emphasized that this latest hack underscores the necessity for self-custody — and consumers should rely on hardware wallets instead of entrusting their funds to exchanges.
The post The Bybit Hack Explained: What Happened, Who Did It, What Happens Next appeared first on Cryptonews.
