Disclaimer: Information found on CryptoreNews is those of writers quoted. It does not represent the opinions of CryptoreNews on whether to sell, buy or hold any investments. You are advised to conduct your own research before making any investment decisions. Use provided information at your own risk.
CryptoreNews covers fintech, blockchain and Bitcoin bringing you the latest crypto news and analyses on the future of money.
What are address poisoning attacks in cryptocurrency and how can they be prevented?
Address poisoning attacks are malicious strategies employed by attackers to redirect traffic, disrupt services, or gain unauthorized access to sensitive information by inserting false data or altering routing tables. These attacks pose a significant threat to data integrity and network security, exploiting vulnerabilities in network protocols.
This article will clarify what address poisoning attacks entail, their various types and repercussions, and how individuals can safeguard themselves against such threats.
Understanding address poisoning attacks in crypto
In the cryptocurrency sector, address poisoning attacks refer to hostile actions where attackers manipulate or deceive users by altering cryptocurrency addresses.
On a blockchain network, these addresses, composed of unique alphanumeric sequences, act as the origin or destination for transactions. Various techniques are employed in these attacks to compromise the integrity and security of cryptocurrency wallets and transactions.
In the crypto domain, address poisoning attacks are primarily aimed at illegally obtaining digital assets or disrupting the seamless functioning of blockchain networks. These attacks may include:
Theft
Attackers may deceive users into sending their funds to malicious addresses through methods such as phishing, transaction interception, or address manipulation.
Disruption
Address poisoning can disrupt the normal functioning of blockchain networks by causing congestion, delays, or interruptions in transactions and smart contracts, thereby diminishing the network’s efficiency.
Deception
Attackers often seek to mislead cryptocurrency users by impersonating well-known figures. This erodes community trust in the network and can lead to erroneous transactions or confusion among users.
Address poisoning attacks underscore the importance of stringent security measures and ongoing vigilance within the cryptocurrency ecosystem to protect digital assets and maintain the overall integrity of blockchain technology.
Related:How to mitigate the security risks associated with crypto payments
Categories of address poisoning attacks
Address poisoning attacks in the crypto space encompass phishing, transaction interception, address reuse exploitation, Sybil attacks, fake QR codes, address spoofing, and vulnerabilities in smart contracts, each presenting distinct risks to users’ assets and network integrity.
Phishing attacks
In the cryptocurrency landscape, phishing attacks are a common form of address poisoning, where malicious actors create counterfeit websites, emails, or communications that closely mimic legitimate entities like cryptocurrency exchanges or wallet providers.
These fraudulent platforms aim to deceive unsuspecting users into revealing their login credentials, private keys, or mnemonic phrases (recovery/seed phrases). Once obtained, attackers can execute unauthorized transactions and gain access to victims’ Bitcoin (BTC) holdings, for instance.
For example, hackers might construct a fake exchange website that closely resembles the authentic one and prompt users to log in. Once they do, the attackers can access customer funds on the legitimate exchange, leading to significant financial losses.
Transaction interception
Another form of address poisoning is transaction interception, where attackers capture valid cryptocurrency transactions and alter the destination address. Funds intended for the legitimate recipient are redirected by changing the recipient address to one controlled by the attacker. This type of attack often involves malware compromising a user’s device or network, or both.
Address reuse exploitation
Attackers monitor the blockchain for instances of address reuse and exploit these occurrences. Reusing addresses can pose security risks as it may expose the address’s transaction history and vulnerabilities. Malicious actors leverage these weaknesses to access user wallets and steal funds.
For instance, if a user consistently receives funds from the same Ethereum address, an attacker might identify this pattern and exploit a flaw in the user’s wallet software to gain unauthorized access to the user’s funds.
Sybil attacks
Sybil attacks involve creating multiple false identities or nodes to exert disproportionate control over a cryptocurrency network’s operations. With this control, attackers can manipulate data, deceive users, and potentially compromise the network’s security.
In the context of proof-of-stake (PoS) blockchain networks, attackers may deploy numerous fraudulent nodes to significantly influence the consensus mechanism, enabling them to alter transactions and potentially double-spend cryptocurrencies.
Fake QR codes or payment addresses
Address poisoning can also occur through the distribution of fake payment addresses or QR codes. Attackers often provide these counterfeit codes in physical form to unsuspecting users, aiming to trick them into sending cryptocurrency to an unintended location.
For example, a hacker might circulate QR codes for cryptocurrency wallets that appear legitimate but contain slight alterations to the encoded address. Users who scan these codes inadvertently send funds to the attacker’s address instead of the intended recipient, resulting in financial losses.
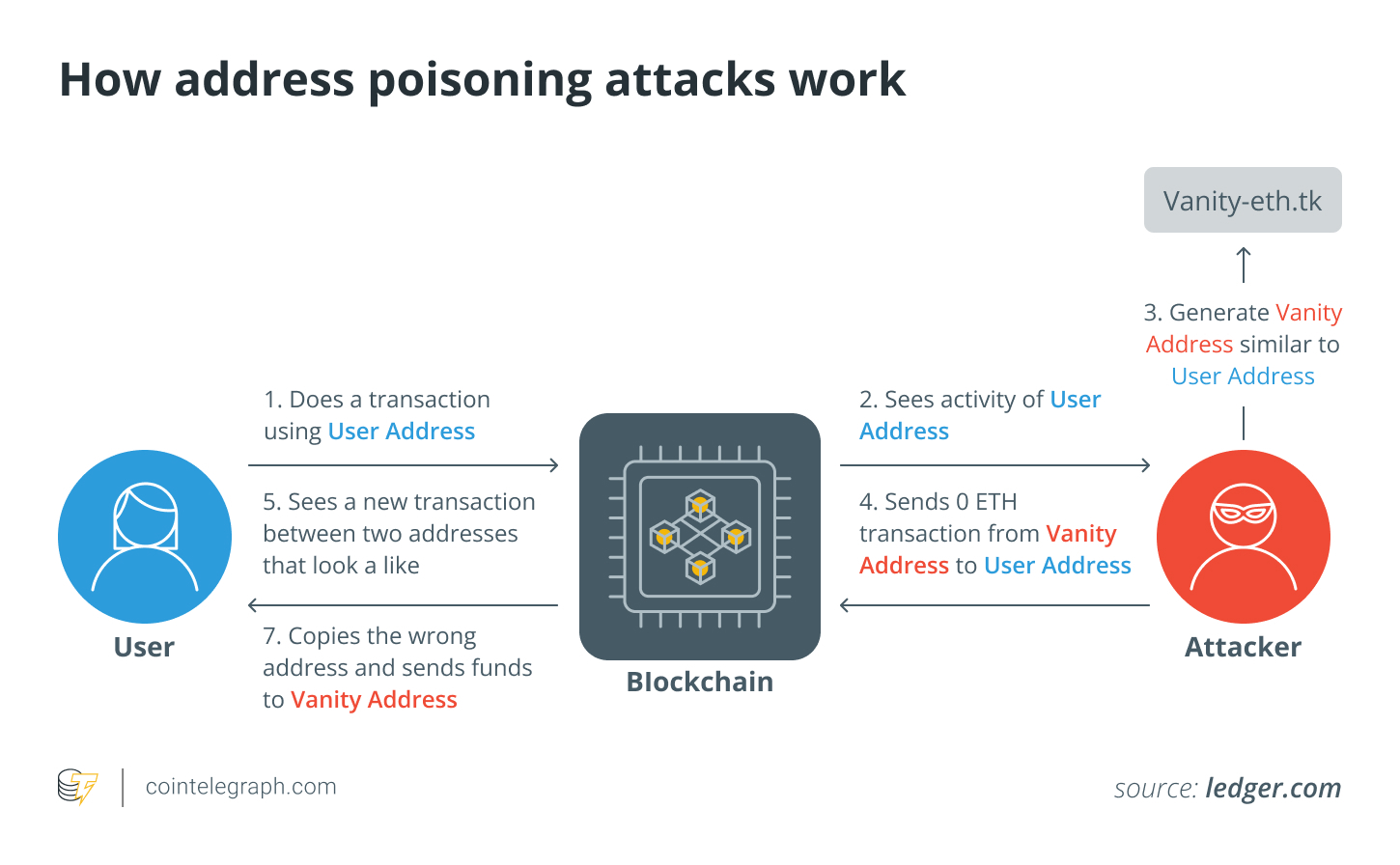
Address spoofing
Address spoofing involves attackers creating cryptocurrency addresses that closely resemble legitimate ones. The objective is to deceive users into sending funds to the attacker’s address rather than the intended recipient’s address. This method relies on the visual similarity between the fake address and the authentic one.
For instance, an attacker might generate a Bitcoin address that closely mimics the donation address of a reputable charity. Unwitting donors may inadvertently send funds to the attacker’s address while attempting to donate to the organization, diverting the funds from their intended purpose.
Smart contract vulnerabilities
Attackers exploit flaws or vulnerabilities in decentralized applications (DApps) or smart contracts on blockchain platforms to execute address poisoning. By manipulating transaction processes, attackers can reroute funds or cause the contract to behave unexpectedly. This can lead to financial losses for users and disruptions in decentralized finance (DeFi) services.
Impacts of address poisoning attacks
Address poisoning attacks can have severe consequences for both individual users and the stability of blockchain networks. These attacks often result in significant financial losses for victims, as attackers may steal cryptocurrency holdings or alter transactions to redirect funds to their own wallets.
In addition to financial losses, these attacks can also diminish trust among cryptocurrency users. If users fall victim to fraudulent schemes or have their assets stolen, their confidence in the security and reliability of blockchain networks and related services may be undermined.
Moreover, certain address poisoning attacks, such as Sybil attacks or the exploitation of smart contract vulnerabilities, can disrupt the normal functioning of blockchain networks, leading to delays, congestion, or unforeseen consequences that impact the entire ecosystem. These effects emphasize the necessity for robust security measures and user awareness in the crypto ecosystem to mitigate the risks associated with address poisoning attacks.
Related: How to put words into a Bitcoin address? Here’s how vanity addresses work
Preventing address poisoning attacks
To safeguard users’ digital assets and ensure the security of blockchain networks, it is essential to prevent address poisoning attacks in the cryptocurrency space. The following strategies may help reduce the risk of becoming a target of such attacks:
Use new addresses
By generating a new crypto wallet address for each transaction, the likelihood of attackers linking an address to an individual’s identity or previous transactions can be minimized. For example, employing hierarchical deterministic (HD) wallets, which create new addresses for each transaction, can reduce the predictability of addresses and mitigate the risk of address poisoning attacks.
Using an HD wallet enhances a user’s protection against address poisoning attacks, as the wallet’s automatic address rotation complicates efforts for hackers to redirect funds.
Utilize hardware wallets
Compared to software wallets, hardware wallets offer a more secure option. They reduce exposure by keeping private keys offline.
Be cautious when sharing public addresses
Individuals should exercise caution when sharing their crypto addresses publicly, particularly on social media platforms, and consider using pseudonyms.
Select reputable wallets
It is crucial to choose well-established wallet providers known for their security features and regular software updates to protect against address poisoning and other attacks.
Regular updates
To remain protected against address poisoning attacks, it is vital to consistently update wallet software with the latest security patches.
Implement whitelisting
Utilize whitelisting to restrict transactions to trusted sources. Some wallets or services allow users to whitelist specific addresses that can send funds to their wallets.
Consider multisig wallets
Multisignature (multisig) wallets require multiple private keys to authorize a transaction. These wallets can provide an additional layer of security by necessitating multiple signatures for transaction approval.
Use blockchain analysis tools
Individuals can monitor and analyze incoming transactions using blockchain analysis tools to identify potentially harmful activities. A common practice known as dusting involves sending seemingly insignificant, small amounts of cryptocurrency to numerous addresses. Analysts can detect potential poisoning attempts by examining these dust transaction patterns.
Unspent transaction outputs (UTXOs) with minimal amounts of cryptocurrency often result from dust transactions. Analysts can identify potentially poisoned addresses by locating UTXOs associated with dust transactions.
Report suspected attacks
Individuals should act promptly in the event of a suspected address poisoning attack by contacting their crypto wallet provider through official support channels and detailing the incident.
Additionally, they can report the incident to relevant law enforcement or regulatory authorities for further investigation and potential legal action if the attack involved significant financial damage or malicious intent. Timely reporting is essential to mitigate potential risks and protect both individual and collective interests within the cryptocurrency ecosystem.
