Disclaimer: Information found on CryptoreNews is those of writers quoted. It does not represent the opinions of CryptoreNews on whether to sell, buy or hold any investments. You are advised to conduct your own research before making any investment decisions. Use provided information at your own risk.
CryptoreNews covers fintech, blockchain and Bitcoin bringing you the latest crypto news and analyses on the future of money.
Recently uncovered Bitcoin wallet vulnerability allowed cybercriminals to take $900K, according to SlowMist.
A recently identified flaw in the Libbitcoin Explorer 3.x library has resulted in the theft of more than $900,000 from Bitcoin users, as reported by blockchain security firm SlowMist. This vulnerability also poses a risk to users of Ethereum, Ripple, Dogecoin, Solana, Litecoin, Bitcoin Cash, and Zcash who utilize Libbitcoin for account generation.
SlowMist Security Alert
Recently, #Distrust uncovered a critical vulnerability impacting cryptocurrency wallets that utilize the #Libbitcoin Explorer 3.x versions. This flaw enables attackers to gain access to wallet private keys by taking advantage of the Mersenne Twister pseudo-random…— SlowMist (@SlowMist_Team) August 10, 2023
Libbitcoin serves as a Bitcoin wallet implementation that developers and validators occasionally use to create Bitcoin (BTC) and other cryptocurrency accounts. As stated on its official website, it is utilized by “Airbitz (mobile wallet), Bitprim (developer interface), Blockchain Commons (decentralized wallet identity), Cancoin (decentralized exchange)” and various other applications. SlowMist did not clarify which applications utilizing Libbitcoin, if any, are impacted by this vulnerability.
Cointelegraph contacted the Libbitcoin Institute via email but had not received a response by the time of publication.
SlowMist identified the cybersecurity group “Distrust” as the original discoverers of the flaw, referred to as the “Milk Sad” vulnerability. This was reported to the CEV cybersecurity vulnerability database on August 7.
The post indicates that the Libbitcoin Explorer has a defective key generation process, enabling attackers to guess private keys. Consequently, attackers exploited this flaw to steal over $900,000 worth of cryptocurrency as of August 10.
SlowMist highlighted that one specific attack resulted in the theft of over 9.7441 BTC (approximately $278,318). The firm asserts that it has “blocked” the address, suggesting that the team has reached out to exchanges to prevent the attacker from liquidating the funds. The team also mentioned that it will continue to monitor the address in case the funds are transferred elsewhere.
Four members of the Distrust team, along with eight freelance security experts who claim to have assisted in identifying the vulnerability, have established an informational website detailing the flaw. They clarified that the loophole arises when users utilize the “bx seed” command to generate a wallet seed. This command “employs the Mersenne Twister pseudorandom number generator (PRNG) initialized with 32 bits of system time,” which lacks adequate randomness and can occasionally yield the same seed for multiple users.
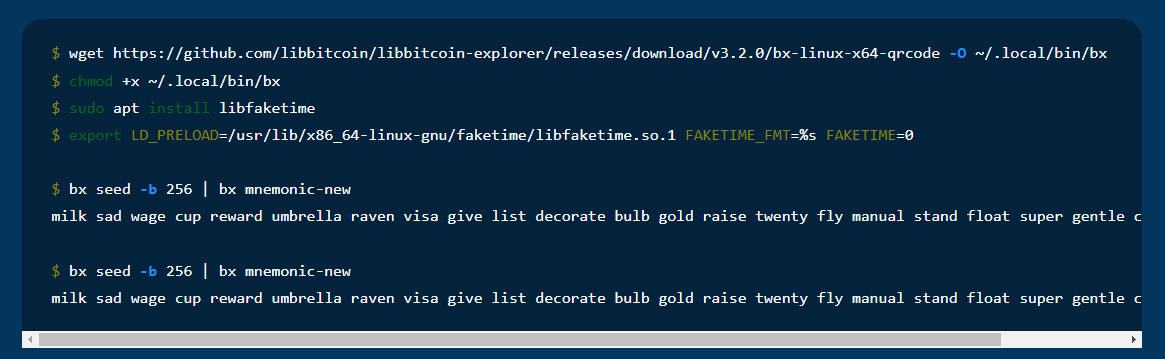 Bx seed command producing the same seed twice. Source: Milk Sad information site
Bx seed command producing the same seed twice. Source: Milk Sad information site
The researchers assert that they uncovered the vulnerability after being contacted by a Libbitcoin user whose BTC had inexplicably disappeared on July 21. When the user reached out to other Libbitcoin users to investigate how the BTC could have vanished, they discovered that other users were also experiencing similar losses.
Wallet vulnerabilities remain a significant concern for crypto users in 2023. More than $100 million was lost in a hack of the Atomic Wallet in June, which was acknowledged by the app’s team on June 22. Cybersecurity certification platform CER published its wallet security rankings in July, indicating that only six out of 45 wallet brands utilize penetration testing to identify vulnerabilities.
