Disclaimer: Information found on CryptoreNews is those of writers quoted. It does not represent the opinions of CryptoreNews on whether to sell, buy or hold any investments. You are advised to conduct your own research before making any investment decisions. Use provided information at your own risk.
CryptoreNews covers fintech, blockchain and Bitcoin bringing you the latest crypto news and analyses on the future of money.
Investigating Stolen Cryptocurrency: The Role of Blockchain Analysis in Fund Recovery
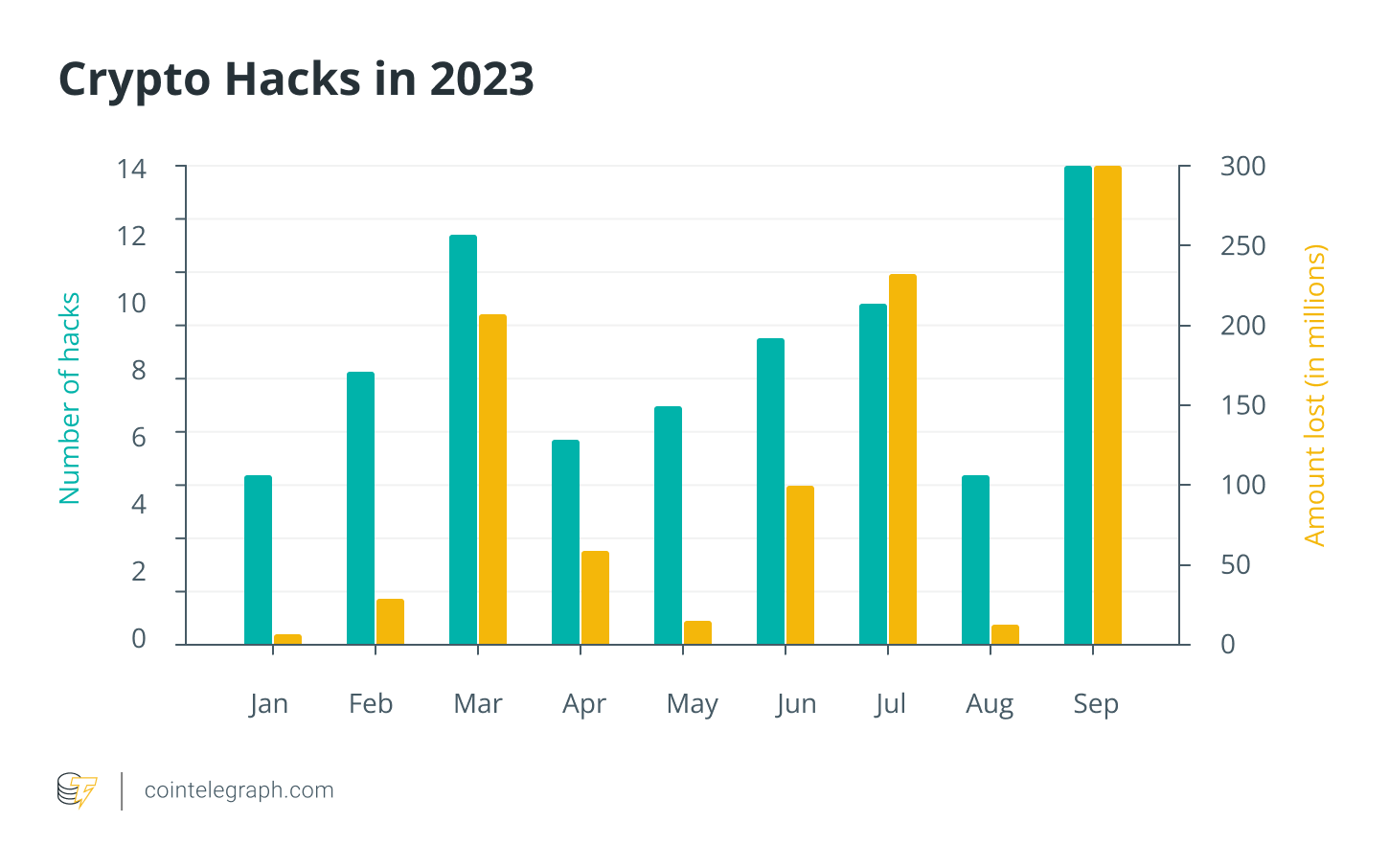
In the fast-paced development of decentralized finance (DeFi) and the wider Web3 environment, security holds critical significance. New threats are constantly arising, making it vital to comprehend attack patterns for effective risk evaluation and reliability assessment. In 2023 alone, more than $990 million was either lost or stolen, as reported by Cointelegraph’s Crypto Hacks database.
This increasing need for security has fostered the growth of a varied ecosystem of Web3 security expertise, which includes decentralized identity solutions and smart contract auditors, all aimed at safeguarding this vibrant digital realm.
Register for the Cointelegraph Research Crypto Hacks Database here
The Lazarus Group, a hacking organization linked to the North Korean state, continues to pose a significant threat. In 2023, Lazarus was accountable for confirmed losses amounting to at least $291 million. As the year advanced into the third quarter, Lazarus remained active, executing an attack on CoinEx that led to losses surpassing $55 million, serving as a stark reminder of the cybersecurity challenges faced.
Enhancing crypto security through blockchain analysis
Moreover, even organizations occasionally find it challenging to fend off potential hacks and exploits. Consequently, individual crypto enthusiasts must acquire skills to perform analysis and research to safeguard their funds. Blockchain analysis involves the investigative process of scrutinizing blockchain transactions to trace illicit activities and recover stolen assets. Here’s how it operates:
- Transaction tracing: Blockchain analysts carefully track blockchain transactions that involve stolen cryptocurrency.
- Address clustering: Analysts categorize related addresses to pinpoint the movement of stolen funds. This clustering aids in understanding how funds transition between wallets.
- Behavioral analysis: Analysts can detect unusual or suspicious activities that may suggest hacking or theft by examining transaction patterns.
- Pattern recognition: Analysts utilize historical data and known attack patterns to identify emerging threats, facilitating early detection and response.
- Regulatory vigilance: Governments globally are advocating for the implementation of stricter Anti-Money Laundering (AML) and Know Your Customer (KYC) regulations in the crypto sector.
- Collaboration: Blockchain analysis frequently involves working alongside law enforcement agencies, exchanges, and other stakeholders to freeze or recover stolen assets.
When probing a cryptocurrency hack, blockchain analysis is one of the tools available to investigators. Open-source intelligence (OSINT) serves as another essential element. Investigators employ OSINT to collect information regarding individuals or entities implicated in the hack. This may involve utilizing tools such as Etherscan, Nansen, Tenderly, Ethective, or Breadcrumbs to gain a clearer understanding of the situation.
By merging blockchain analysis with OSINT, investigators can create a thorough overview of the hack, potentially identifying the culprits and recovering stolen assets more efficiently.
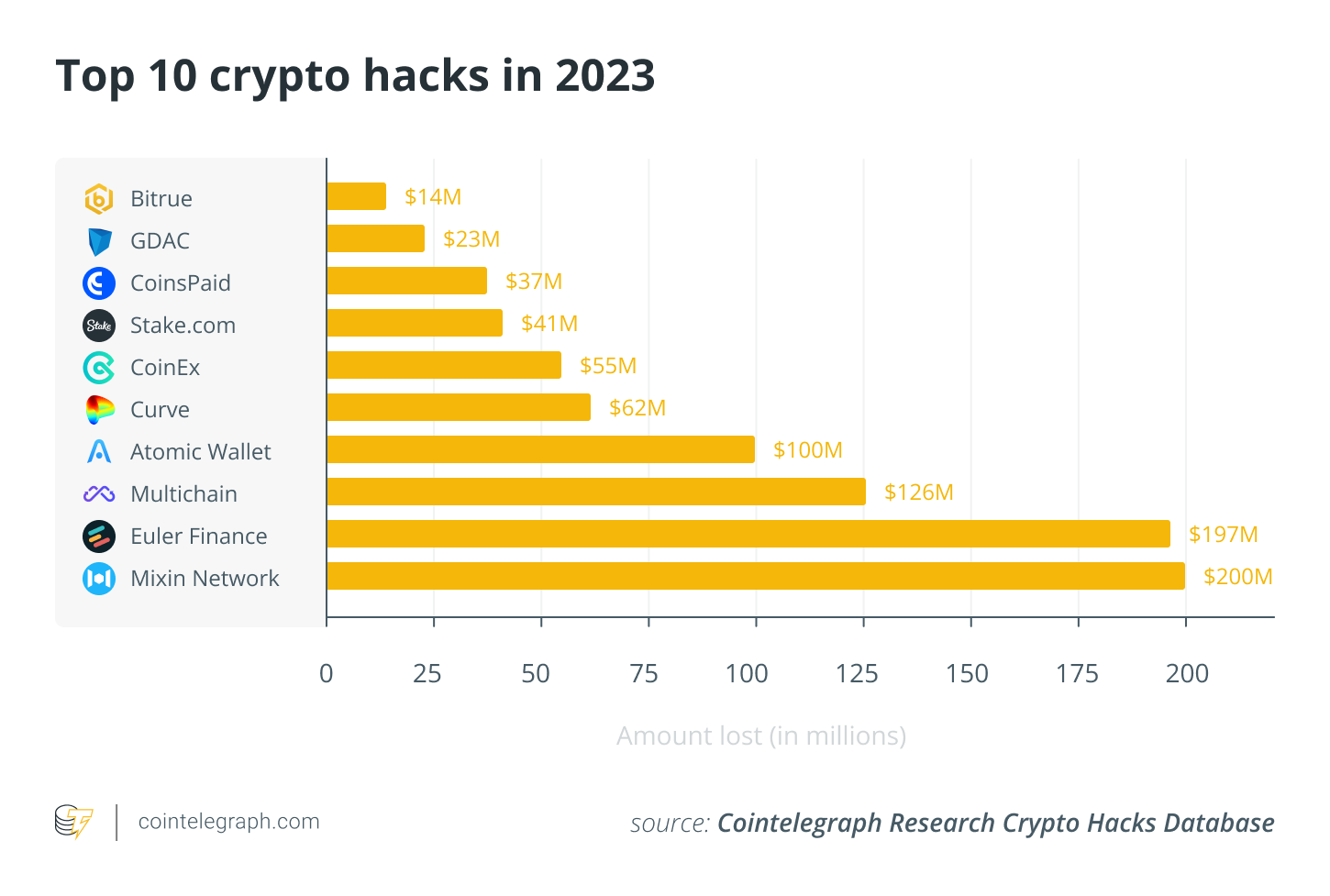
In a significant instance, the individual responsible for the Curve Finance exploit, which led to over $61 million in cryptocurrency losses on July 30th, has returned approximately $8.9 million in cryptocurrency to Alchemix Finance and Curve Finance. Interestingly, the attacker’s intention was not to avoid capture but to maintain the integrity of the compromised protocols. The exploit, which took advantage of a reentrancy bug, impacted several pools, including Alchemix Finance’s alETH-ETH, JPEG’d pETH-ETH, and Metronome sETH-ETH pools. Although the returned funds constitute roughly 15% of the total drained, this event underscores the complex ethical and motivational dynamics present in the crypto landscape following security breaches.
On-chain data remains an invaluable investigative asset, unique to the blockchain and crypto asset domain. Thanks to the foundational distributed ledger technology, it offers all Web3 participants an exceptional perspective on asset movements, transaction tracking, and robust analytical capabilities. Maximize these opportunities by exploring the Cointelegraph Research Crypto Hacks database, an essential resource for obtaining comprehensive insights into recent security incidents and emerging threats. Discover how this powerful tool can enable you to safeguard your crypto assets and stay ahead of potential risks.
The Cointelegraph Research team
Cointelegraph’s Research division consists of some of the finest talents in the blockchain sector. Merging academic rigor with practical, hard-earned experience, the researchers on the team are dedicated to delivering the most precise and insightful content available in the market.
With decades of collective experience in traditional finance, business, engineering, technology, and research, the Cointelegraph Research team is ideally positioned to effectively utilize its combined expertise.
The views expressed in this article are for general informational purposes only and are not intended to provide specific advice or recommendations for any individual or on any particular security or investment product.
