Disclaimer: Information found on CryptoreNews is those of writers quoted. It does not represent the opinions of CryptoreNews on whether to sell, buy or hold any investments. You are advised to conduct your own research before making any investment decisions. Use provided information at your own risk.
CryptoreNews covers fintech, blockchain and Bitcoin bringing you the latest crypto news and analyses on the future of money.
Guide to Utilizing a Cryptocurrency Hardware Wallet
Investing in cryptocurrencies is commonly recognized as risky due to the volatility of the crypto market, regulatory challenges, and notable incidents involving hacks, scams, and fraudulent activities. Chainalysis’ midyear report on cryptocurrency-related crimes in 2022 indicated that around $1.9 billion in cryptocurrency was stolen through various hacking incidents and fraudulent activities, compared to less than $1.2 billion at the same time in 2021.
Safely storing and managing cryptocurrency assets presents its own challenges, necessitating that traders educate themselves on optimal options. A crypto hardware wallet, a form of cold storage, is a physical device designed to securely keep cryptocurrencies offline, offering additional security for those who possess significant amounts of crypto and wish to protect their holdings over the long term.
This article will explore what a hardware wallet is, how to utilize one, and the advantages of hardware wallets compared to software wallets, while also addressing the ongoing question: Should you store your crypto coins in a hardware wallet? Additionally, it will provide information on the hardware wallets available for securely storing your crypto assets.
Related: How to reduce the security risks linked to crypto payments
What is a crypto hardware wallet
Crypto wallets can generally be divided into two main categories: hot wallets and cold wallets. Hot wallets are software-based crypto wallets that are connected to the internet, whereas cold wallets are physical devices. Cold wallets are regarded as a more secure storage solution than hot software wallets, as they are not connected to the internet and do not interact with potentially vulnerable software or web viruses. Among cold wallets, hardware crypto wallets are viewed as one of the safest methods for storing cryptocurrencies.
A hardware wallet is a physical device that typically resembles a USB drive or a small plug-in device, designed to securely store cryptocurrencies and other digital assets such as non-fungible tokens (NFTs). Hardware wallets do not actually hold cryptocurrency; instead, they keep the private keys that grant access to the stored digital assets.
Users can check the price, model, and specifications according to their needs. Most hardware wallets support Bitcoin (BTC), Ether (ETH), stablecoins like Tether (USDT) and USD Coin (USDC), as well as other popular digital assets such as Ripple’s XRP (XRP) and Litecoin (LTC).
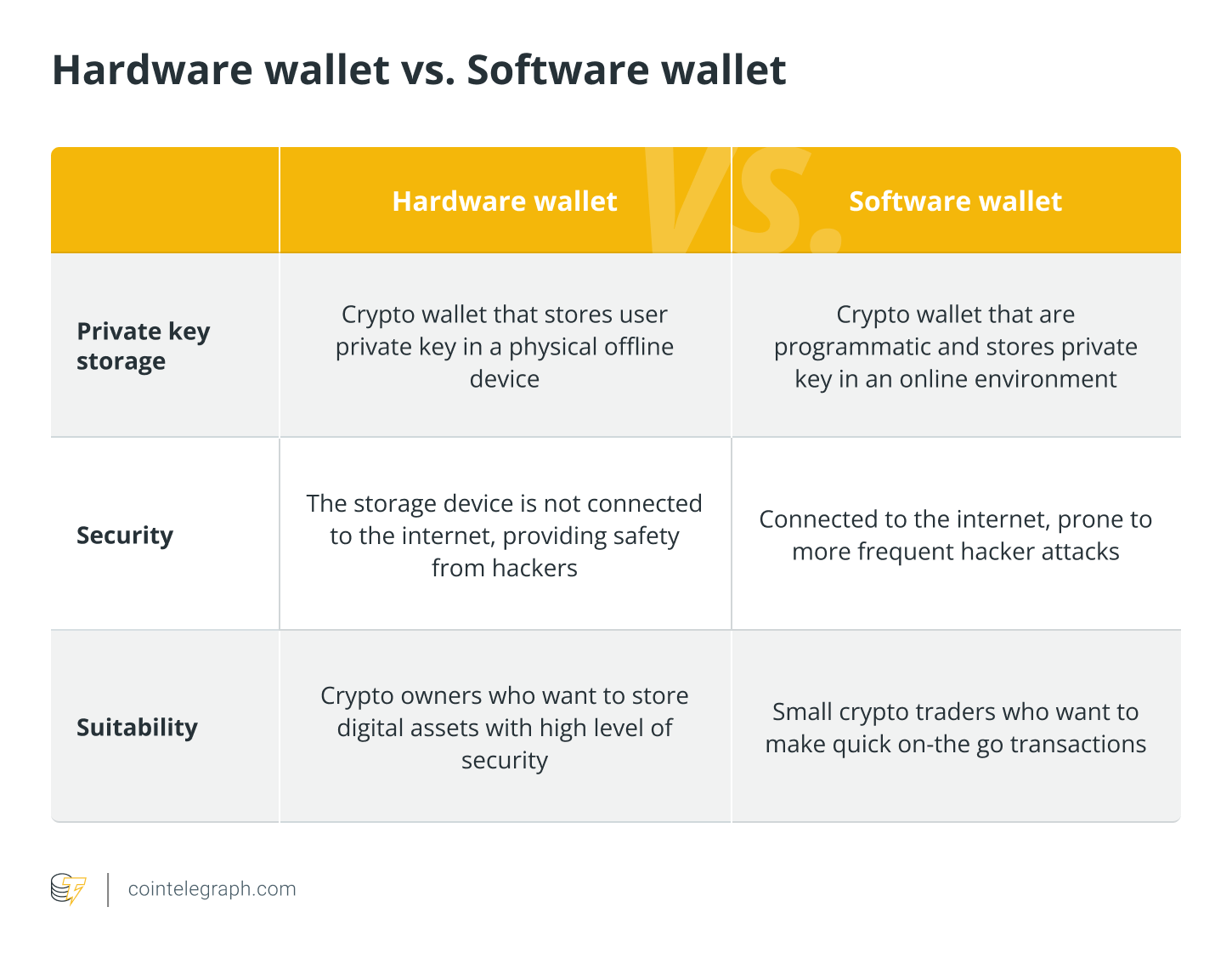
Hardware wallet vs Software wallet
While software wallets offer convenience and ease of use, hardware wallets are recognized for their secure storage capabilities. A solid understanding of the differences between the two options, user needs, and the level of digital asset custody required can assist users in making informed decisions regarding their wallet preferences.
How does a hardware wallet work
Before delving into how a hardware wallet functions, it is important to have some knowledge about crypto wallet keys.
Public and private crypto wallet keys
Cryptocurrency data resides on the blockchain, and crypto wallets store this information. Unlike fiat currency, this data on the blockchain determines ownership of the assets.
Each crypto wallet contains a pair of keys for access — a private key and a public key. The public key is similar to a bank account number and can be accessed by anyone. Conversely, the private key is akin to an ATM PIN and must be kept secure by the user.
Private keys provide access to cryptocurrency funds and must be protected by the owner, as they should not be shared with anyone. They consist of a unique combination of letters and numbers, acting as digital signatures or passwords that grant access to and control over cryptocurrency holdings. Hardware crypto wallets typically store these private keys, which are essential for signing transactions.
Hardware wallet self custody
When users keep their cryptocurrencies on a centralized exchange (CEX), they effectively transfer custody and control of their private keys and digital assets to the exchange, using login credentials provided by the CEX. This means that users depend on the exchange to securely hold and manage their funds on their behalf, making them susceptible to scams, hacks, and other security threats if the exchange is compromised.
In contrast, hardware wallets provide users with complete control and self-custody over their digital assets. Users retain their private keys and are not dependent on third-party custodians or exchanges. To conduct cryptocurrency transactions using hardware wallets, the private key must be “signed.” This signing process occurs within the hardware wallet itself via a cryptocurrency bridge, which connects the hardware wallet to the blockchain.
The hardware wallet sends the signed transaction to the bridge, which then broadcasts the signed transaction to the blockchain network. Notably, at no point during this entire process does the user’s private key leave the hardware wallet, ensuring safety and security.
Related: What is a Bitcoin Wallet? A beginner’s guide to storing BTC
How to use a hardware crypto wallet
The specific steps and procedures may vary slightly based on the particular hardware wallet. Users should refer to the manufacturer’s instructions and adhere to security practices to learn how to operate a specific hardware wallet.
The following are some common steps to understand how hardware wallets can be utilized:
Step 1: Purchase and install software
Acquire a crypto hardware wallet from reputable manufacturers such as Ledger, Trezor, and Ngrave — and/or their authorized resellers. Ensure that it is sealed and free from tampering. Visit the official website of the hardware wallet manufacturer, then download and install the wallet software on desktop or mobile devices. Be sure to review the recommendations for device specifications — operating system, processor, etc.
Step 2: Connect the hardware wallet
Connect the hardware wallet to a desktop or mobile device using the provided USB cable or the appropriate wireless connection (Bluetooth or NFC). Follow the on-screen instructions to set up the hardware wallet. This includes selecting a PIN or passphrase, creating a backup recovery seed phrase, and securely storing the seed in multiple offline locations. The recovery seed is vital for restoring access to funds if the hardware wallet is lost or damaged.
Step 3: Add funds and transact
Within the wallet software, find the option to receive or deposit cryptocurrencies. Copy the public address displayed or scan the QR code to add the desired amount of cryptocurrency to this public address from an exchange or another wallet.
To send cryptocurrencies from the hardware wallet, select the option to send or transfer funds, and enter the recipient’s address and the amount to send. Confirm the transaction details on the hardware wallet’s screen.
Step 4: Confirm, sign and verify transactions
After confirming the transaction details on the hardware wallet, you will be prompted to provide additional authorization by entering a PIN or passphrase. The hardware wallet will then sign the transaction with the private key stored within it, and the funds will be transacted. Monitor the progress of the transactions using blockchain explorers or within the wallet software. Verify that the transaction has been confirmed and added to the blockchain.
It is crucial to remember to securely disconnect the hardware wallet from the desktop or mobile device after completing the transaction and ensure its safekeeping.
Popular hardware wallets
Hardware cryptocurrency wallets have gained popularity among crypto enthusiasts, investors, and crypto whales. These include wallets such as Ledger and Trezor, which provide a secure and user-friendly method for storing and managing digital assets. Other well-known names in the market include Ellipal, CoolWallet, SafePal, and Ngrave, among others. Additionally, certain hardware wallets like Ledger offer staking and other earning opportunities through their Ledger Live app.
The advantages of hardware wallets in securing cryptocurrencies became even more evident in 2022 due to the crypto exchange failures of FTX, Celsius, BlockFi, and Vault, which led to the loss of access to billions of dollars. Consequently, hardware wallet providers like Ledger and Trezor experienced unprecedented sales as crypto holders sought storage safety and reliability.
Are hardware crypto wallets secure
For anyone who has been involved in the crypto space for a considerable time, there is a common adage: “Not your keys, not your crypto.” Essentially, this phrase serves as a reminder for cryptocurrency users to take charge of their own security and ensure the protection of their digital assets. It advocates for the use of hardware wallets and other cold storage solutions to keep private keys offline and safeguarded from potential cyber threats.
Crypto hardware wallets are widely acknowledged as secure solutions for storing, managing, and taking custody of one’s digital assets and cryptocurrencies. While no security measure can guarantee absolute safety, hardware wallets offer additional layers of security and protections for storing cryptocurrencies.
