Disclaimer: Information found on CryptoreNews is those of writers quoted. It does not represent the opinions of CryptoreNews on whether to sell, buy or hold any investments. You are advised to conduct your own research before making any investment decisions. Use provided information at your own risk.
CryptoreNews covers fintech, blockchain and Bitcoin bringing you the latest crypto news and analyses on the future of money.
ZachXBT exposes a cryptocurrency laundering operation with a monthly turnover of $1 million., 2026/04/09 13:47:54

The anonymous blockchain investigator ZachXBT has examined a leak of internal data linked to North Korean IT specialists and uncovered a cryptocurrency laundering scheme that processes approximately $1 million monthly.
According to ZachXBT, the scheme involves 390 users. Funds are transferred using cryptocurrency wallets and subsequently converted into fiat currency. Since the end of 2025, over $3.5 million in cryptocurrencies has flowed through tracked addresses associated with this network.
At the core of the scheme is an internal platform described as a hub for money transfers. Here, employees report their earnings, share experiences of successful thefts, and receive instructions, as stated by the anonymous crypto detective. He suggested that the hub serves two purposes: it acts as a messaging tool and a coordination point for payments.
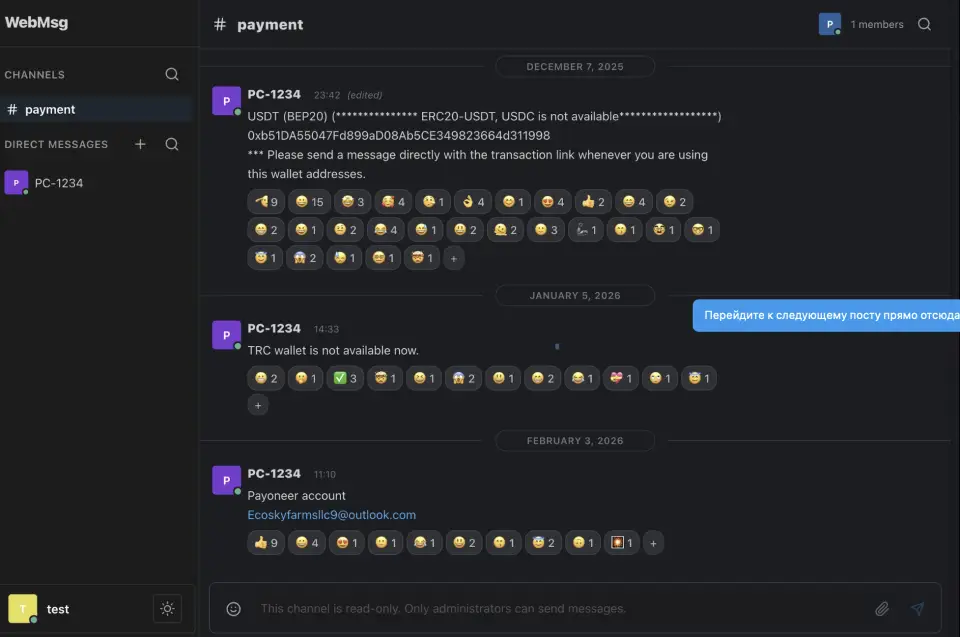
According to ZachXBT, the stolen cryptocurrency typically originates from exchanges or service platforms and is then withdrawn to front wallets. In several instances, the cryptocurrency is converted into fiat through intermediaries, including Chinese bank accounts and payment systems.
A dedicated administrative account handles the confirmation of transfers and the distribution of credentials for further movement of funds. Specific wallets in the scheme led the blockchain investigator to addresses previously associated with the activities of North Korean hacking groups. At least one wallet has been frozen by Tether, the issuer of the USDT stablecoin.
In user communications, Korean names, geographical references in North Korea, and coded identifiers of groups are mentioned, according to ZachXBT. The correspondence references three North Korean organizations that have been sanctioned by the U.S., Sobaeksu, Saenal, and Songkwang, which have been accused of working for the North Korean government.

Participants in the scheme create and utilize fake identities to secure remote work, as established by ZachXBT through an analysis of browser histories, chat communications, and internal notes. Participants coordinated their responses to job postings using counterfeit credentials and deepfakes, later sharing information with one another.
The network, in addition to its cryptocurrency laundering function, also serves as a training platform for fraudsters. Educational materials on developing and debugging malware are disseminated within it, as noted by ZachXBT.
Meanwhile, the blockchain detective believes that the network does not reach the scale of more advanced North Korean groups. Nevertheless, it operates in a coordinated and active manner, consistently processing large volumes of digital assets, stated the crypto researcher. To support the claim of the network’s “unprofessionalism,” ZachXBT pointed out that some participants neglected the security of their accounts—ten accounts on the hub platform used the default password “1234.”
Previously, MetaMask security specialist Taylor Monahan stated that North Korean experts have infiltrated cryptocurrency companies and decentralized finance (DeFi) projects for at least seven years, with many aiming to hack platforms.
