Disclaimer: Information found on CryptoreNews is those of writers quoted. It does not represent the opinions of CryptoreNews on whether to sell, buy or hold any investments. You are advised to conduct your own research before making any investment decisions. Use provided information at your own risk.
CryptoreNews covers fintech, blockchain and Bitcoin bringing you the latest crypto news and analyses on the future of money.
Zunami Protocol reports that stablecoin pools were compromised, with an estimated loss of $2.1 million.
The decentralized finance protocol Zunami Protocol has confirmed that it has faced an attack on its “zStables” pool located on Curve Finance.
According to blockchain security firm PeckShield, more than $2.1 million was taken from Zunami’s Curve Pool on August 13, attributing the breach to a price manipulation problem. Another blockchain security company, Ironblocks, reported a similar estimate.
Hi @ZunamiProtocol Today's hack results in a loss exceeding $2.1 million, involving two hack transactions:
– tx1: https://t.co/jsOmPT62mk
– tx2: https://t.co/u7YOvoS0R9
This is a price manipulation issue that can be exploited through donations to inaccurately assess the price as demonstrated in the… https://t.co/yqwMVy0pCA pic.twitter.com/OfrDni7KtE— PeckShield Inc. (@peckshield) August 14, 2023
PeckShield identified the exploit on Curve at 10:47 UTC on August 13, which Zunami confirmed approximately 20 minutes later.
Zunami stated that the collateral within the Curve pools remains secure and that an investigation into the matter is currently underway.
It seems that zStables have been subjected to an attack. The collateral remains secure, and we are investigating the situation.
— Zunami Protocol (@ZunamiProtocol) August 13, 2023
It is currently suspected that a flash loan price manipulation attack may have affected Zunami’s zETH and UZD.
Related: Curve Finance pledges to compensate users following $62M hack
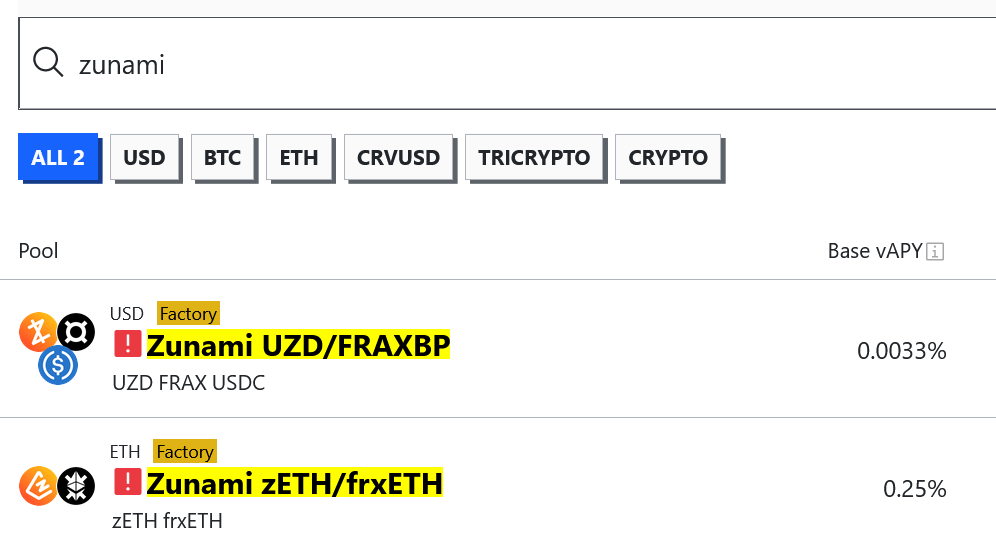 Zunami’s zETH and UZD Curve pools have been marked with red exclamation points on Curve. Source: Curve Finance
Zunami’s zETH and UZD Curve pools have been marked with red exclamation points on Curve. Source: Curve Finance
Zunami operates as a decentralized revenue aggregator protocol that enables users to stake stablecoins for yield, with its largest stable pools located on Curve.
Cointelegraph attempted to contact Zunami for a statement but did not receive an immediate reply.
Magazine: $3.4B of Bitcoin in a popcorn tin — The Silk Road hacker’s story
This is an evolving story, and additional information will be provided as it becomes available.
