Disclaimer: Information found on CryptoreNews is those of writers quoted. It does not represent the opinions of CryptoreNews on whether to sell, buy or hold any investments. You are advised to conduct your own research before making any investment decisions. Use provided information at your own risk.
CryptoreNews covers fintech, blockchain and Bitcoin bringing you the latest crypto news and analyses on the future of money.
The shift to post-quantum technology cannot be delayed any further.
Google’s recent study may jeopardize the entire bitcoin supply and the core of digital trust, according to Pruden.

A whitepaper released yesterday by Google Quantum AI indicates that a fast-clock quantum computer, similar in design to their existing Willow chip, could obtain a private key from an exposed public key in roughly nine minutes. Bitcoin processes a block every 10 minutes.
This suggests an average of a one-minute window during which the system could operate while an attacker could seize live transactions directly from the mempool before confirmation. That multi-trillion-dollar interval signifies that not only Satoshi’s coins but the entire Bitcoin supply now and in the future is vulnerable.
For years, the industry’s stance on quantum threats has been encapsulated in the phrase “we’ll address it when it becomes a reality.” Even among those who regarded this threat seriously, many believed that the first genuine danger to Bitcoin was at least a decade away and would manifest as “long-range” attacks on inactive assets. This paper, among a series of rapid advancements, renders that view untenable.
This research introduces a dramatic shift that hastens the timeline significantly. The ramifications for the digital asset ecosystem are serious. If we do not initiate an urgent upgrade effort immediately, digital assets as we currently understand them may become unfeasible.
The pace of change is accelerating
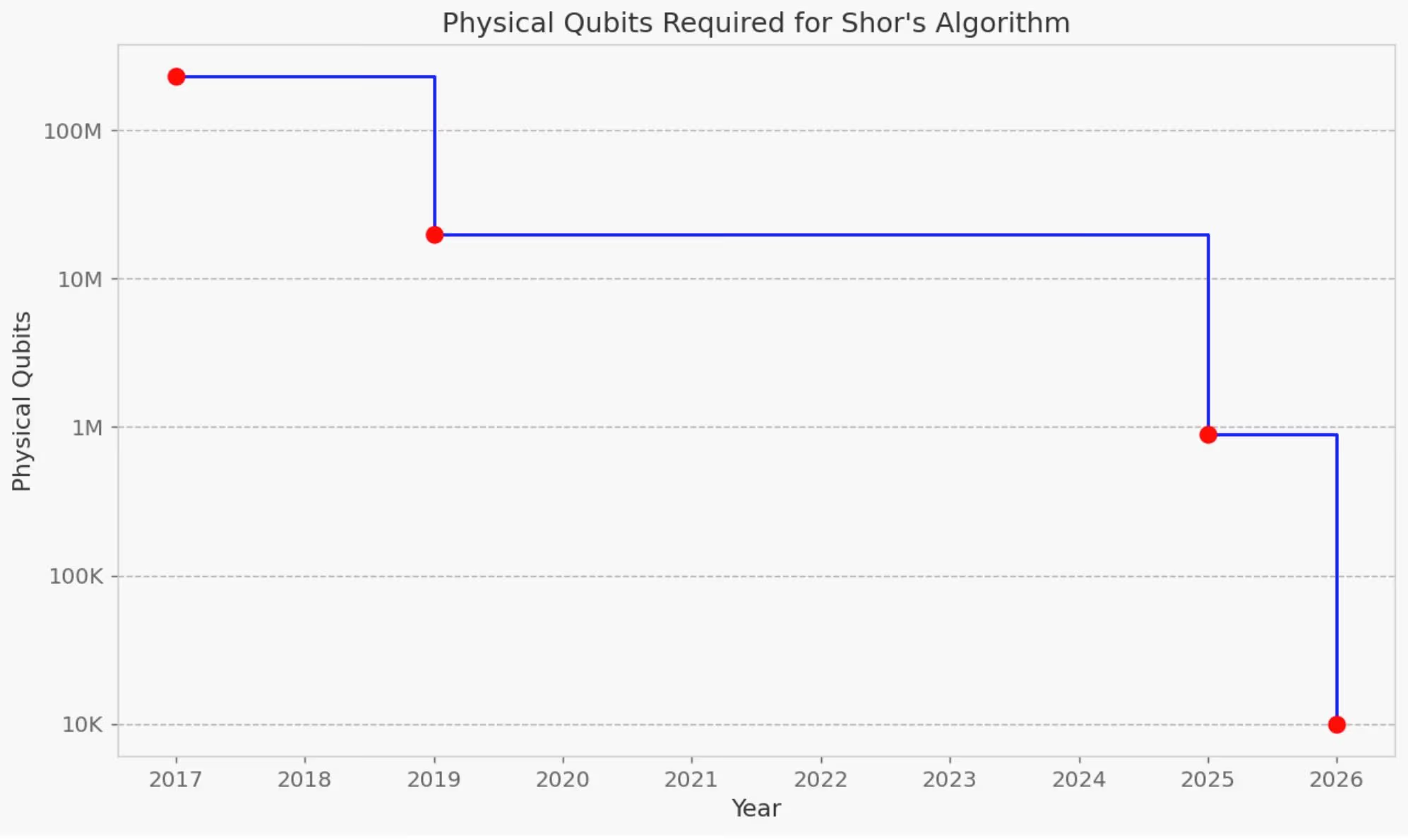
Historically, projections indicated that tens of millions of physical qubits executing a trillion error-corrected operations would be necessary to pose a threat to Bitcoin. However, these estimates were based not on the elliptic-curve cryptography utilized by Bitcoin but rather on an older algorithm known as RSA-2048.
Google’s whitepaper dismantles those previous resource estimates by presenting an architecture capable of solving the 256-bit Elliptic Curve Discrete Logarithm Problem (ECDLP) specifically applied to Bitcoin.
This paper reduces the physical requirement to fewer than half a million qubits and decreases the number of operations by several orders of magnitude. It accomplishes this with just 1,200 logical qubits at an error rate of 0.1%, a benchmark that seems achievable in the near future. Google has reportedly accelerated its own quantum timelines to 2029.
More crucially, the architecture employed (superconducting) features rapid physical clock speeds. This implies that not only “lost” or dormant coins are at risk; every single active Bitcoin transaction could be susceptible to a quantum attacker seizing it directly from the mempool.
However, the findings from Google are not an isolated incident; they form part of two converging advancements.
Researchers from Oratomic unveiled a parallel breakthrough utilizing neutral-atom hardware. By employing high-rate quantum low-density parity check (qLDPC) codes, they demonstrated that Shor’s algorithm can be executed at cryptographically relevant scales with approximately 10,000 to 22,000 reconfigurable atomic qubits. What once necessitated millions of qubits has been significantly compressed in just a few years across two distinct technological paths.
Multiple tech trees with one target
How is it that quantum computing has made little headway for an extended period, yet we are now observing the timeline condense so rapidly? The answer lies in small, iterative advancements in physical fidelity, error correction, control architectures, and algorithm design, which are creating a feedback loop that amplifies progress.
Faster machines facilitate improved error-correction research, lowering the resource requirements for the next generation of machines and hastening timelines at non-linear rates.
Perhaps the most perilous misunderstanding is the belief that quantum advancements depend on a singular “miracle” breakthrough in one specific area of physics. The quantum threat does not hinge on one moonshot that could falter. Superconducting, photonic, neutral-atom, and ion-trap architectures embody entirely distinct engineering roadmaps, physics, and funding sources. Only one of these needs to succeed for quantum computing to achieve cryptographic significance.
While it is accurate that none of these systems has yet been fully validated at scale, their validation is increasingly evident, with reputable entities and substantial investment backing them. Are we truly willing to gamble with trillions of dollars at stake?
The clock is ticking on migration
The tendency to postpone until a cryptographically relevant quantum computer is publicly verified fundamentally misinterprets how decentralized networks upgrade. Transitioning a decentralized network like Bitcoin is not akin to flipping a switch on an enterprise server. Trillions of dollars in assets are at stake, and all networks must undertake an unprecedented upgrade to implement new cryptography at the foundational level.
Regrettably, addressing one issue introduces new challenges. Post-Quantum Cryptography (PQC) necessitates considerably larger digital signatures, thus increasing bandwidth, storage, and computing demands. Executing this will require a hard fork, and achieving the necessary community consensus will be a challenging and politically sensitive endeavor.
Even after consensus is achieved, the logistical complexities of transferring the assets are immense. At Bitcoin’s current transaction pace, migrating the network to post-quantum addresses would take several months—assuming the network processed nothing else and every block was filled.
If we delay until Q-Day (the day a quantum computer relevant to cryptography is publicly confirmed) to commence this process, it may be too late. Digital signatures will have already lost their authority, and any attempts to retroactively resolve the issue could lead to severe financial fluctuations. In a worst-case scenario, there could be competing forks, fractured institutional trust, and a crisis of provenance for trillions of dollars in assets.
Urgency, not panic
This is not a call for alarm; it is a call for pragmatism. Executives and institutions that currently hold a significant portion of the circulating bitcoin supply, stablecoin issuers, and major protocol teams must recognize that the risk landscape has fundamentally transformed. The quantum threat is no longer a theoretical exercise for academics; it is an engineering reality progressing rapidly.
We must act without delay. The global community requires proactive migration strategies, tools to establish post-quantum ownership, and a collective industry mandate to upgrade before the first silent theft occurs. The quantum adversary is approaching and will not announce their presence. However, we can prepare. We must coordinate this upgrade today to ensure the survival of the foundation of digital trust into the quantum era.
