Disclaimer: Information found on CryptoreNews is those of writers quoted. It does not represent the opinions of CryptoreNews on whether to sell, buy or hold any investments. You are advised to conduct your own research before making any investment decisions. Use provided information at your own risk.
CryptoreNews covers fintech, blockchain and Bitcoin bringing you the latest crypto news and analyses on the future of money.
A Solana function intended for user convenience enabled assailants to siphon over $270 million from Drift.
The breach did not stem from a flaw in Drift’s code. It utilized “durable nonces,” a legitimate feature of Solana transactions, to pre-sign administrative transfers weeks prior to their execution, circumventing the protocol’s multisig security in mere minutes.

Key points:
- An attacker exploited a legitimate feature known as ‘durable nonces’ to siphon at least $270 million from the Drift Protocol on Solana, rather than taking advantage of a code flaw or compromised keys.
- By obtaining two deceptive approvals from Drift’s five-member Security Council multisig, the attacker pre-signed transactions that remained valid for over a week and subsequently used them to gain control of the protocol in a matter of minutes.
- The incident impacted all user deposits within Drift and funneled assets through NEAR, Backpack, Wormhole, and Tornado Cash, highlighting the growing threat posed by social engineering and operational shortcomings—particularly regarding the management of durable nonces—in decentralized finance.
The breach of Drift Protocol was not a conventional hack.
No code flaw or private key compromise was discovered. There was no flash loan exploit or manipulated oracle involved either.
Rather, the attacker utilized a valid Solana feature, ‘durable nonces,’ to deceive Drift’s Security Council into pre-approving transactions that would be executed weeks later, in a manner and context that the signers did not foresee.
The outcome was a loss of at least $270 million that was executed in under a minute but took more than a week to prepare.
Understanding durable nonces and their purpose
In Solana, each transaction is accompanied by a ‘recent blockhash,’ which acts as a timestamp validating that the transaction was generated recently. This blockhash becomes invalid after approximately 60 to 90 seconds. If the transaction is not submitted to the network within that timeframe, it is rendered invalid. This serves as a safety mechanism to prevent old, stale transactions from being replayed.
Durable nonces bypass this safety mechanism. They substitute the expiring blockhash with a fixed ‘nonce,’ a unique code held in a designated on-chain account, which keeps the transaction valid indefinitely until it is submitted.
This feature exists for valid reasons. Hardware wallets, offline signing arrangements, and institutional custody solutions require the ability to prepare and authorize transactions without the obligation to submit them within 90 seconds.
However, transactions that are valid indefinitely pose a challenge. If someone can secure a signature today, that transaction can be executed weeks or even months later, according to the system’s hardcoded rules. The signer cannot cancel their approval once it is granted, except by manually advancing the nonce account, which most users do not monitor.
The attacker’s approach
Drift’s protocol was overseen by a ‘Security Council multisig,’ a mechanism where multiple individuals (in this case, five) share control, requiring a minimum of two approvals for any action. Multisigs are a common security practice in decentralized finance, based on the premise that compromising a single individual is insufficient to misappropriate funds.
However, the attacker did not need to compromise anyone’s keys. They only required two signatures, which they seem to have acquired through what Drift refers to as “unauthorized or misrepresented transaction approvals,” indicating that the signers likely believed they were endorsing a standard transaction.
Here is the timeline disclosed by Drift in a post on Thursday via X.
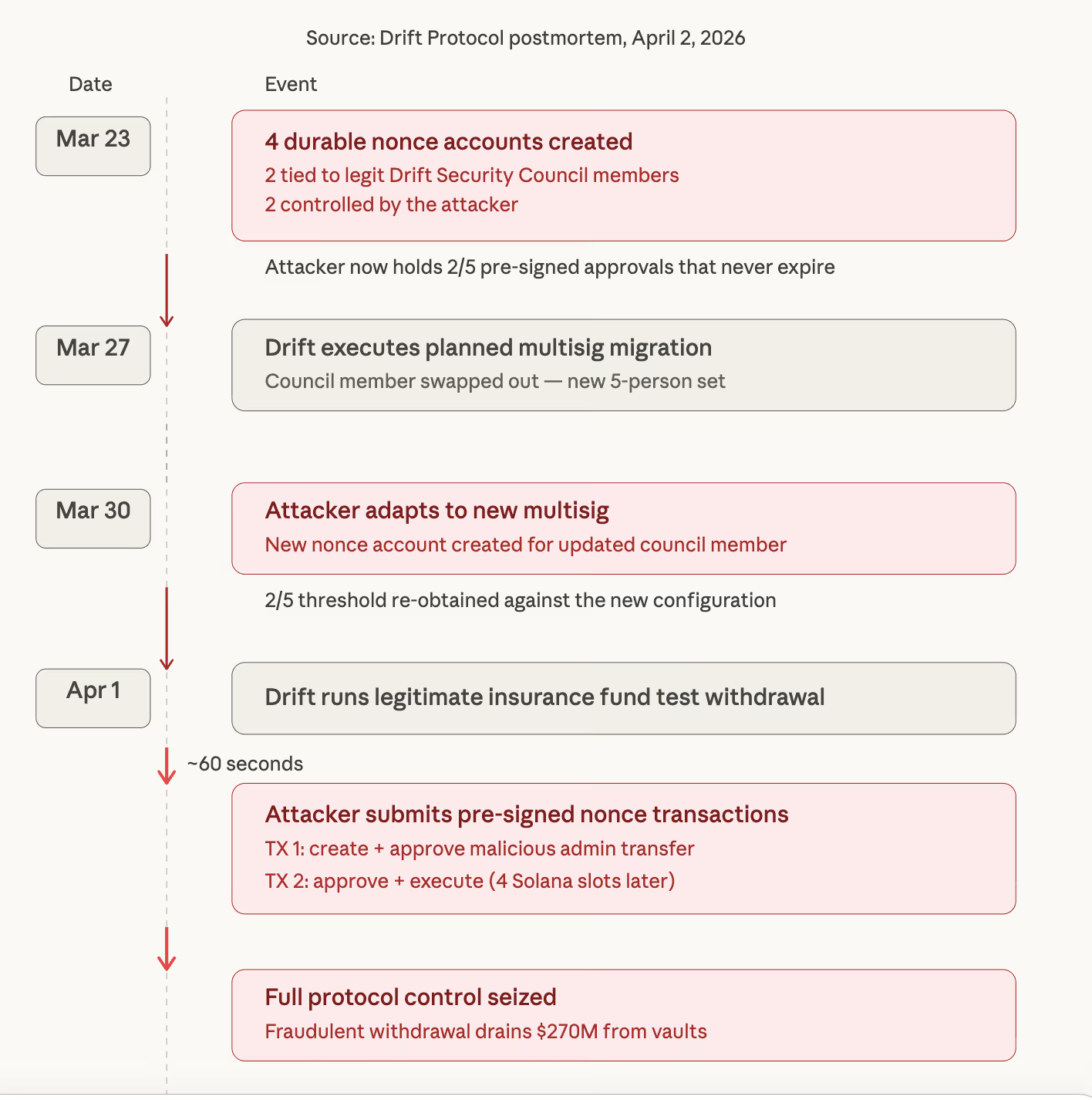
On March 23, four durable nonce accounts were established. Two were linked to legitimate Drift Security Council members, while two were under the attacker’s control. This suggests that the attacker had already secured valid signatures from two of the five council members, locked into durable nonce transactions that would not expire.
On March 27, Drift conducted a planned Security Council migration to replace a council member. The attacker adjusted their strategy. By March 30, a new durable nonce account was created, associated with a member of the updated multisig, indicating that the attacker had regained the necessary two-of-five approval threshold under the new configuration.
On April 1, the attacker initiated the execution.
Initially, Drift performed a legitimate test withdrawal from its insurance fund. Roughly one minute later, the attacker submitted the pre-signed durable nonce transactions. Two transactions, four slots apart on the Solana blockchain, were sufficient to create and authorize a malicious admin transfer, followed by its approval and execution.
In mere minutes, the attacker gained complete control over Drift’s protocol-level permissions. They used this authority to implement a fraudulent withdrawal mechanism and drain the vaults.
Details of what was stolen and its destination
Onchain analysts monitored the movement of funds in real time. The compilation of stolen assets, prepared by security researcher Vladimir S., amounted to approximately $270 million across a variety of tokens.
The most significant single category was $155.6 million in JPL tokens, followed by $60.4 million in USDC, $11.3 million in CBBTC (Coinbase wrapped bitcoin), $5.65 million in USDT, $4.7 million in wrapped ether, $4.5 million in DSOL, $4.4 million in WBTC, $4.1 million in FARTCOIN, and smaller values in JUP, JITOSOL, MSOL, BSOL, EURC, and others.
